- Blockstream deployed the first quantum-resistant transactions on Bitcoin’s Liquid sidechain
- Users can opt into post-quantum protection without changing Bitcoin’s core protocol
- Debate continues on urgency, but research suggests future quantum risks are real
Blockstream Research has rolled out something that, at first glance, might not look flashy — but it’s actually pretty significant. The team claims to have executed the first live transactions on a Bitcoin sidechain secured by post-quantum cryptography, which is a fancy way of saying… they’re preparing for a future where today’s encryption might not hold up.
This move comes as concerns around quantum computing slowly creep from theory into something more real. The fear isn’t immediate collapse or anything dramatic, but rather that, over time, powerful quantum machines could break the cryptographic systems protecting crypto wallets. And if that happens, well, the implications get serious pretty fast.
What Blockstream Actually Built (And Why It’s Different)
Following a recent Google research paper that explored vulnerabilities across crypto systems — wallets, validation, even cross-chain bridges — Blockstream seems to have moved ahead with a practical response. They deployed a post-quantum signature scheme called SHRINCS on Bitcoin’s Liquid sidechain.
What’s interesting is how they did it. Instead of changing Bitcoin’s core rules (which is always messy and slow), they used Simplicity, their smart contract language, to layer in new security conditions. So users can choose to lock funds with quantum-resistant signatures if they want. No forced upgrades, no waiting for consensus… just opt-in protection.
The research also outlined four key risks tied to sidechains: forged transaction signatures, fake block signatures, compromised confidential transactions, and vulnerabilities in bridges moving assets between chains. Not all of these are solved yet — but some are already being addressed.
Progress Is Real, But It’s Uneven
Right now, transaction-level protection is live. That’s the part they’ve actually deployed and tested in real conditions, with real funds. But other areas, like block signing and confidential asset protection, are still being worked on — some in testing, others still in development.
There’s also ongoing research into securing Bitcoin as it moves across bridges, which is… honestly one of the more fragile areas in crypto overall. It’s not a solved problem yet, but at least it’s being actively explored rather than ignored.
Meanwhile, Google’s paper added a bit more urgency to the conversation. It suggested that a sufficiently advanced quantum computer could crack private keys in just days. Even more concerning, it mentioned possible “mempool attacks,” where transactions could be intercepted before they’re even confirmed. That part, if it ever becomes real, could be messy.
Debate Continues, But the Clock Is Ticking
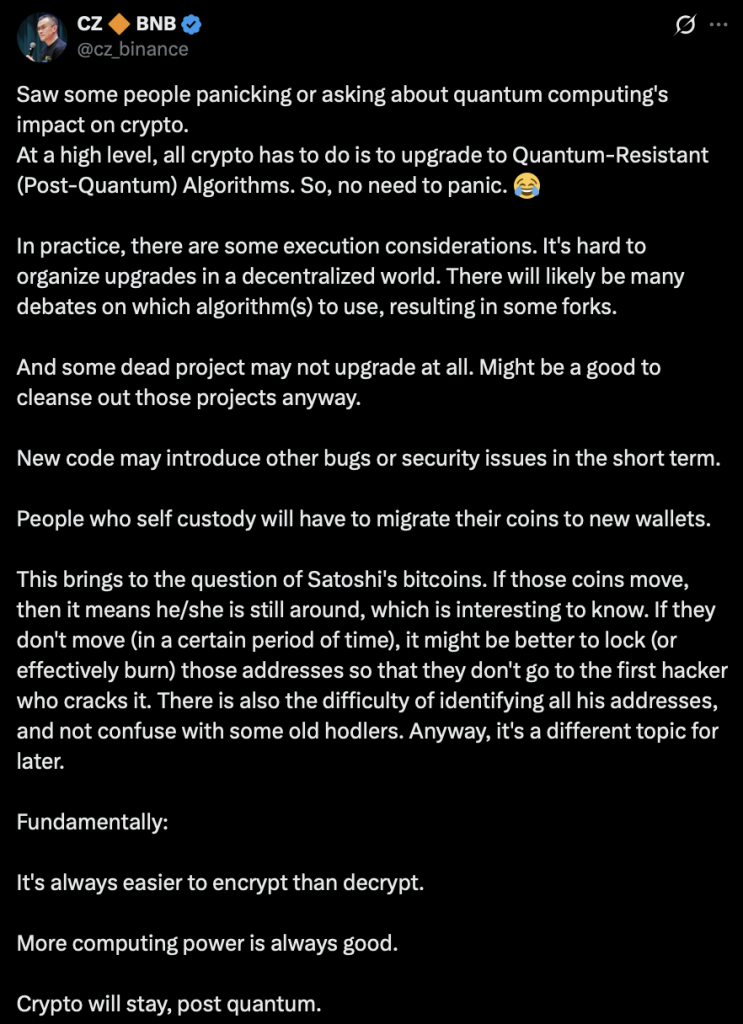
Not everyone thinks this is an immediate threat, though. Changpeng Zhao, former Binance CEO, recently downplayed the urgency, saying there’s no need to panic. His view is that crypto networks can simply upgrade to quantum-resistant algorithms when the time comes.
Still, there are some awkward edge cases. CZ pointed out that around one million BTC — believed to belong to Satoshi — are stored in older wallet formats that wouldn’t survive a quantum attack. If those coins are never moved, they could eventually need to be locked or removed from circulation entirely. It’s a strange scenario, but not impossible.
Blockstream isn’t stopping here either. They’re also developing a related system called SHRIMPS, which produces much smaller post-quantum signatures — about three times smaller than current government standards. That matters for Bitcoin, where block space is limited and efficiency is everything. A formal proposal is already in the works.
A Glimpse of Bitcoin’s Future Security
What’s live on Liquid today isn’t the final solution — not even close. But it’s proof that post-quantum security can actually function in a real-world environment, not just in theory or lab conditions.
And maybe that’s the bigger takeaway. The industry isn’t waiting for quantum computing to become a crisis before reacting. It’s starting, slowly, unevenly, but still… starting to build defenses ahead of time. Whether that’s early or just barely on time, we’ll probably find out later.