- Bitrefill suffered a cyberattack likely tied to North Korea’s Lazarus Group
- Hackers accessed wallets, infrastructure, and limited customer data
- The incident highlights growing state-backed threats in crypto
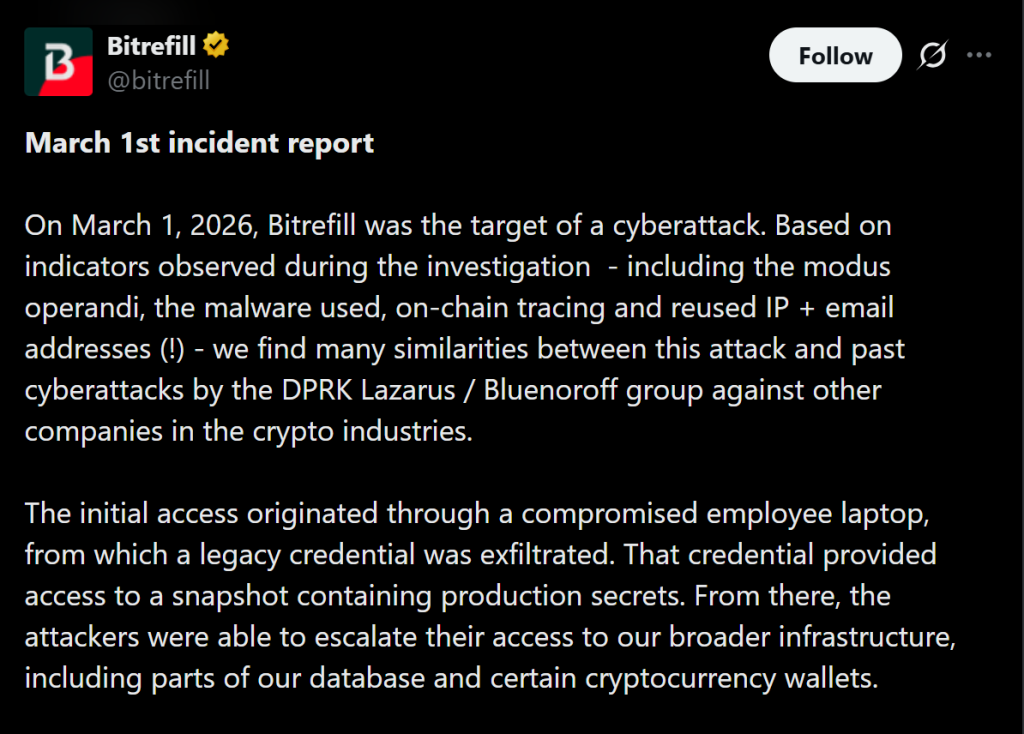
Crypto e-commerce platform Bitrefill has confirmed it was targeted in a cyberattack earlier this month, with strong indicators pointing to North Korea’s Lazarus Group. The attack reportedly began on March 1 and involved tactics, malware, and infrastructure patterns similar to previous operations linked to the group.
According to the company, attackers gained access through a compromised employee laptop, a method commonly used by Lazarus. From there, they were able to drain some hot wallets, interact with vendor systems, and probe internal infrastructure. While the total financial loss has not been disclosed, Bitrefill said it will absorb any damages using its own operational capital.
How the Attack Unfolded
The breach went beyond just wallets. Bitrefill revealed that parts of its broader infrastructure were accessed, including sections of its database and certain crypto systems.
Hackers retrieved around 18,500 purchase records, exposing limited customer data such as email addresses, crypto payment addresses, and metadata like IP information. Roughly 1,000 records may have also revealed encrypted customer names, prompting the company to notify affected users.
Despite this, Bitrefill emphasized that there is no evidence the attackers extracted the full database. The activity appeared more exploratory, aimed at identifying valuable assets like crypto funds and gift card inventory.
Lazarus Group Remains the Biggest Threat
The suspected involvement of Lazarus highlights a growing trend in crypto security. The North Korean-backed group has become one of the most active and successful hacking operations in the space.
In 2025 alone, entities linked to the group were responsible for an estimated $2.02 billion in stolen crypto. That includes major incidents like the $1.5 billion Bybit exploit, one of the largest hacks in the industry’s history.
Their methods have also evolved. Beyond technical exploits, Lazarus is known to infiltrate companies through social engineering, including posing as IT workers to gain internal access.
Limited KYC Exposure but Ongoing Risks
Bitrefill noted that most of its services do not require mandatory KYC, which helped limit the exposure of sensitive personal data. In cases where identity verification is required, the data is handled by external providers rather than stored internally.
This likely reduced the potential damage from the breach. Still, the incident raises ongoing concerns about how crypto companies manage infrastructure access and employee security.
The company has since worked with multiple cybersecurity firms to contain the attack and restore operations. Systems were temporarily taken offline, but services, payments, and sales volumes have now returned to normal.
A Reminder of Structural Risk in Crypto
This attack is another reminder that crypto’s biggest vulnerabilities are often operational, not just technical. Even as blockchain systems themselves remain secure, the surrounding infrastructure continues to be a target.
State-backed actors are increasingly focused on crypto due to its liquidity and global accessibility. As the industry grows, so does the sophistication of these threats.
For users and companies alike, the takeaway is clear. Security is no longer just about wallets and keys, it’s about the entire system surrounding them.