- FBI arrested John Daghita over a $46M crypto theft from U.S. Marshals wallets
- The suspect is linked to a contractor managing seized government crypto
- Investigators say insider access may pose greater risks than hackers
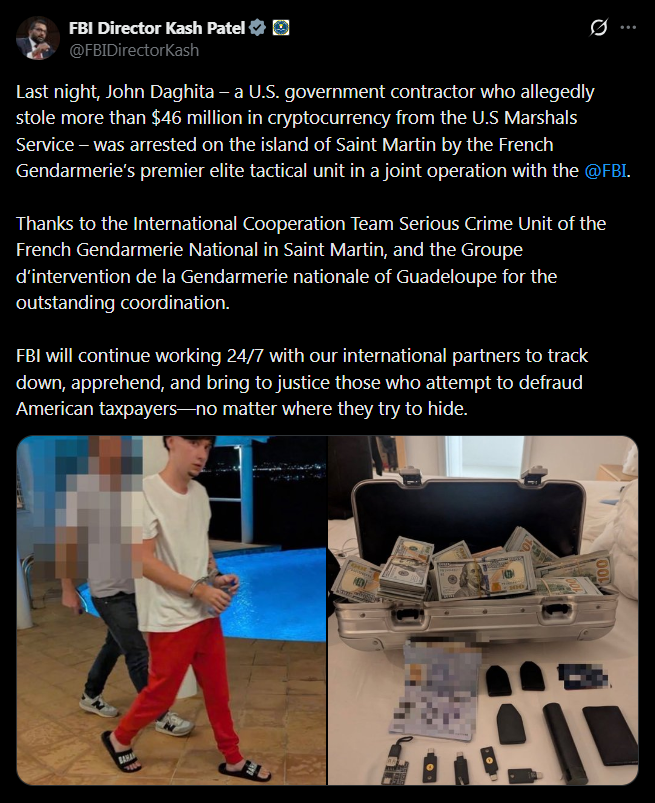
A strange and troubling crypto crime case has unfolded after the FBI arrested John Daghita for allegedly stealing around $46 million in cryptocurrency from wallets controlled by the U.S. Marshals Service. The funds were part of the government’s reserve of seized digital assets, which are typically collected from criminal investigations and held in custody by federal authorities. Instead of an external breach, investigators believe the assets were moved directly from government-controlled wallets to a personal address.
Authorities say the suspect allegedly attempted to launder the funds through multiple crypto transactions after transferring them out of government custody. The method used in this case appears very different from traditional cyberattacks. Rather than exploiting software vulnerabilities, the theft seems to involve direct access to the wallets themselves, which raises uncomfortable questions about internal security practices.
Contractor Ties Raise Questions About Crypto Custody
One of the most striking details in the investigation is the suspect’s connection to a government contractor. Daghita is the son of the CEO of Command Services & Support (CMDSS), a Virginia-based firm that works with the U.S. Marshals Service to help manage and dispose of seized cryptocurrency assets. That relationship is now under intense scrutiny as investigators examine how the alleged access may have occurred.
If authorities confirm that internal access was used to move the funds, the incident could expose a major vulnerability in how institutions safeguard digital assets. Governments and financial organizations often focus heavily on defending against external cyberattacks. Yet insider access can sometimes bypass those security layers entirely.
Blockchain Analysis Helped Identify the Suspect
Ironically, the transparency of blockchain technology may have played a key role in identifying the alleged thief. On-chain investigator ZachXBT reportedly first spotted suspicious activity involving wallets associated with government-controlled funds. The transactions eventually pointed toward wallets believed to be connected to Daghita, who allegedly used the online alias “Lick.”

The investigation quickly escalated once those links became clearer. Authorities ultimately tracked the suspect internationally and carried out an arrest operation in Saint Martin. French law enforcement agencies assisted the FBI in detaining the suspect as the investigation continued to unfold.
The Case Highlights a Growing Insider Threat
Crypto critics frequently argue that digital assets are difficult to track or inherently insecure. This case appears to demonstrate the opposite. Blockchain records provided investigators with a transparent trail that helped trace the movement of funds and identify potential suspects.
The larger issue exposed by the case may not be technological vulnerabilities but human ones. Even sophisticated custody systems can fail if individuals with access choose to misuse it. Governments and institutions may invest heavily in cybersecurity tools, yet insider risk can still remain one of the most difficult threats to control.
Crypto Security Often Comes Down to Human Trust
The lesson emerging from this incident is relatively straightforward. Organizations can build advanced custody frameworks, contract specialized firms, and deploy modern security infrastructure. But if internal access controls are weak, those systems may still be vulnerable.
In many ways, the case highlights a fundamental reality about digital asset security. The technology itself is often transparent and traceable. The real uncertainty lies in how people manage access to it.